Code to support TCP and TLS server/client. More...
#include "asterisk.h"#include "asterisk/tcptls.h"#include "asterisk/iostream.h"#include <fcntl.h>#include <netinet/in.h>#include <openssl/asn1.h>#include <openssl/crypto.h>#include <openssl/err.h>#include <openssl/opensslconf.h>#include <openssl/opensslv.h>#include <openssl/safestack.h>#include <openssl/ssl.h>#include <openssl/x509.h>#include <openssl/x509v3.h>#include <openssl/bio.h>#include <openssl/dh.h>#include <openssl/pem.h>#include <openssl/ec.h>#include <pthread.h>#include <signal.h>#include <sys/socket.h>#include <sys/stat.h>#include "asterisk/app.h"#include "asterisk/astobj2.h"#include "asterisk/compat.h"#include "asterisk/config.h"#include "asterisk/io.h"#include "asterisk/lock.h"#include "asterisk/logger.h"#include "asterisk/netsock2.h"#include "asterisk/pbx.h"#include "asterisk/utils.h"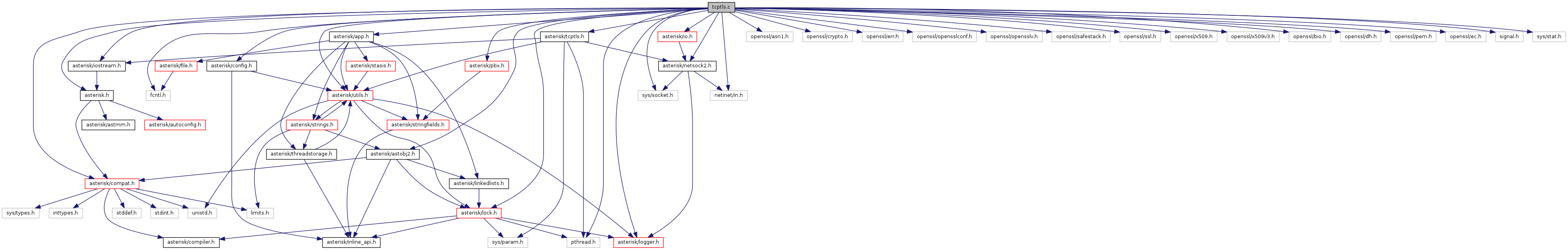
Go to the source code of this file.
Macros | |
| #define | SSL_CTRL_SET_ECDH_AUTO 94 |
Functions | |
| static int | __ssl_setup (struct ast_tls_config *cfg, int client) |
| static void | __ssl_setup_certs (struct ast_tls_config *cfg, const size_t cert_file_len, const char *key_type_extension, const char *key_type) |
| int | ast_ssl_setup (struct ast_tls_config *cfg) |
| Set up an SSL server. More... | |
| void | ast_ssl_teardown (struct ast_tls_config *cfg) |
| free resources used by an SSL server More... | |
| struct ast_tcptls_session_instance * | ast_tcptls_client_create (struct ast_tcptls_session_args *desc) |
| struct ast_tcptls_session_instance * | ast_tcptls_client_start (struct ast_tcptls_session_instance *tcptls_session) |
| attempts to connect and start tcptls session, on error the tcptls_session's ref count is decremented, fd and file are closed, and NULL is returned. More... | |
| void | ast_tcptls_close_session_file (struct ast_tcptls_session_instance *tcptls_session) |
| Closes a tcptls session instance's file and/or file descriptor. The tcptls_session will be set to NULL and it's file descriptor will be set to -1 by this function. More... | |
| void * | ast_tcptls_server_root (void *data) |
| void | ast_tcptls_server_start (struct ast_tcptls_session_args *desc) |
| This is a generic (re)start routine for a TCP server, which does the socket/bind/listen and starts a thread for handling accept(). More... | |
| void | ast_tcptls_server_stop (struct ast_tcptls_session_args *desc) |
| Shutdown a running server if there is one. More... | |
| int | ast_tls_read_conf (struct ast_tls_config *tls_cfg, struct ast_tcptls_session_args *tls_desc, const char *varname, const char *value) |
| Used to parse conf files containing tls/ssl options. More... | |
| static int | check_tcptls_cert_name (ASN1_STRING *cert_str, const char *hostname, const char *desc) |
| static void * | handle_tcptls_connection (void *data) |
| creates a FILE * from the fd passed by the accept thread. This operation is potentially expensive (certificate verification), so we do it in the child thread context. More... | |
| static void | session_instance_destructor (void *obj) |
| static void | write_openssl_error_to_log (void) |
Detailed Description
Code to support TCP and TLS server/client.
Definition in file tcptls.c.
Macro Definition Documentation
◆ SSL_CTRL_SET_ECDH_AUTO
| #define SSL_CTRL_SET_ECDH_AUTO 94 |
Referenced by __ssl_setup().
Function Documentation
◆ __ssl_setup()
|
static |
Definition at line 382 of file tcptls.c.
References __ssl_setup_certs(), ast_debug, ast_log, AST_SSL_DISABLE_TLSV1, AST_SSL_DISABLE_TLSV11, AST_SSL_DISABLE_TLSV12, AST_SSL_SERVER_CIPHER_ORDER, AST_SSL_SSLV2_CLIENT, AST_SSL_SSLV3_CLIENT, AST_SSL_TLSV1_CLIENT, AST_SSL_VERIFY_CLIENT, ast_strlen_zero, ast_test_flag, ast_verb, ast_tls_config::cafile, ast_tls_config::capath, ast_tls_config::certfile, ast_tls_config::cipher, ast_tls_config::enabled, ast_tls_config::flags, LOG_ERROR, LOG_WARNING, NULL, options, ast_tls_config::pvtfile, S_OR, SSL_CTRL_SET_ECDH_AUTO, ast_tls_config::ssl_ctx, and write_openssl_error_to_log().
Referenced by ast_ssl_setup(), and ast_tcptls_client_start().
◆ __ssl_setup_certs()
|
static |
Definition at line 362 of file tcptls.c.
References ast_log, ast_strdupa, ast_tls_config::certfile, LOG_WARNING, ast_tls_config::ssl_ctx, and write_openssl_error_to_log().
Referenced by __ssl_setup().
◆ ast_ssl_setup()
| int ast_ssl_setup | ( | struct ast_tls_config * | cfg | ) |
Set up an SSL server.
- Parameters
-
cfg Configuration for the SSL server
- Return values
-
1 Success 0 Failure
Definition at line 570 of file tcptls.c.
References __ssl_setup().
Referenced by __ast_http_load(), __init_manager(), and reload_config().
◆ ast_ssl_teardown()
| void ast_ssl_teardown | ( | struct ast_tls_config * | cfg | ) |
free resources used by an SSL server
- Note
- This only needs to be called if ast_ssl_setup() was directly called first.
- Parameters
-
cfg Configuration for the SSL server
Definition at line 575 of file tcptls.c.
References NULL, and ast_tls_config::ssl_ctx.
Referenced by sip_tcptls_client_args_destructor(), unload_module(), and websocket_client_args_destroy().
◆ ast_tcptls_client_create()
| struct ast_tcptls_session_instance* ast_tcptls_client_create | ( | struct ast_tcptls_session_args * | desc | ) |
Definition at line 615 of file tcptls.c.
References ast_tcptls_session_args::accept_fd, ao2_alloc, ao2_cleanup, ast_bind(), ast_debug, ast_iostream_from_fd(), ast_log, ast_sockaddr_cmp(), ast_sockaddr_copy(), ast_sockaddr_is_any(), ast_sockaddr_is_ipv6(), ast_sockaddr_isnull(), ast_sockaddr_setnull(), ast_sockaddr_stringify(), ast_str_create, ast_tcptls_session_instance::client, desc, errno, error(), ast_tcptls_session_args::local_address, LOG_ERROR, ast_tcptls_session_args::name, NULL, ast_tcptls_session_args::old_address, ast_tcptls_session_instance::overflow_buf, ast_tcptls_session_instance::parent, ast_tcptls_session_args::remote_address, ast_tcptls_session_instance::remote_address, session_instance_destructor(), ast_tcptls_session_instance::stream, and ast_tcptls_session_args::worker_fn.
Referenced by app_exec(), sip_prepare_socket(), and websocket_client_connect().
◆ ast_tcptls_client_start()
| struct ast_tcptls_session_instance* ast_tcptls_client_start | ( | struct ast_tcptls_session_instance * | tcptls_session | ) |
attempts to connect and start tcptls session, on error the tcptls_session's ref count is decremented, fd and file are closed, and NULL is returned.
Definition at line 585 of file tcptls.c.
References __ssl_setup(), ast_tcptls_session_args::accept_fd, ao2_ref, ast_connect(), ast_fd_clear_flags, ast_log, ast_sockaddr_stringify(), desc, ast_tls_config::enabled, errno, handle_tcptls_connection(), LOG_ERROR, ast_tcptls_session_args::name, NULL, ast_tcptls_session_instance::parent, ast_tcptls_session_args::remote_address, and ast_tcptls_session_args::tls_cfg.
Referenced by _sip_tcp_helper_thread(), app_exec(), and websocket_client_connect().
◆ ast_tcptls_close_session_file()
| void ast_tcptls_close_session_file | ( | struct ast_tcptls_session_instance * | tcptls_session | ) |
Closes a tcptls session instance's file and/or file descriptor. The tcptls_session will be set to NULL and it's file descriptor will be set to -1 by this function.
Definition at line 839 of file tcptls.c.
References ast_debug, ast_iostream_close(), NULL, and ast_tcptls_session_instance::stream.
Referenced by _sip_tcp_helper_thread(), ast_http_create_response(), ast_http_send(), handle_tcptls_connection(), httpd_helper_thread(), and sip_prepare_socket().
◆ ast_tcptls_server_root()
| void* ast_tcptls_server_root | ( | void * | data | ) |
Definition at line 280 of file tcptls.c.
References ast_tcptls_session_args::accept_fd, ao2_alloc, ao2_ref, ast_accept(), ast_fd_clear_flags, ast_iostream_from_fd(), ast_log, ast_pthread_create_detached_background, ast_sockaddr_copy(), ast_sockaddr_stringify(), ast_str_create, ast_wait_for_input(), ast_tcptls_session_instance::client, desc, errno, handle_tcptls_connection(), LOG_ERROR, NULL, ast_tcptls_session_instance::overflow_buf, ast_tcptls_session_instance::parent, ast_tcptls_session_args::periodic_fn, ast_tcptls_session_args::poll_timeout, ast_tcptls_session_instance::remote_address, session_instance_destructor(), and ast_tcptls_session_instance::stream.
◆ ast_tcptls_server_start()
| void ast_tcptls_server_start | ( | struct ast_tcptls_session_args * | desc | ) |
This is a generic (re)start routine for a TCP server, which does the socket/bind/listen and starts a thread for handling accept().
- Version
- 1.6.1 changed desc parameter to be of ast_tcptls_session_args type
Definition at line 685 of file tcptls.c.
References ast_tcptls_session_args::accept_fd, ast_tcptls_session_args::accept_fn, ast_bind(), ast_calloc, ast_debug, ast_free, ast_log, ast_pthread_create_background, AST_PTHREADT_NULL, ast_read_textfile(), ast_sd_get_fd(), ast_sha1_hash(), ast_sockaddr_cmp(), ast_sockaddr_copy(), ast_sockaddr_is_ipv6(), ast_sockaddr_isnull(), ast_sockaddr_setnull(), ast_sockaddr_stringify(), ast_socket_nonblock, ast_strdup, ast_tls_config::cafile, ast_tls_config::cahash, ast_tls_config::capath, ast_tls_config::certfile, ast_tls_config::certhash, ast_tls_config::cipher, errno, error(), ast_tls_config::flags, ast_tcptls_session_args::local_address, LOG_ERROR, ast_tcptls_session_args::master, ast_tcptls_session_args::name, NULL, ast_tcptls_session_args::old_address, ast_tcptls_session_args::old_tls_cfg, ast_tls_config::pvtfile, ast_tls_config::pvthash, str, and ast_tcptls_session_args::tls_cfg.
Referenced by __ast_http_load(), __init_manager(), and reload_config().
◆ ast_tcptls_server_stop()
| void ast_tcptls_server_stop | ( | struct ast_tcptls_session_args * | desc | ) |
Shutdown a running server if there is one.
- Version
- 1.6.1 changed desc parameter to be of ast_tcptls_session_args type
Definition at line 849 of file tcptls.c.
References ast_tcptls_session_args::accept_fd, ast_debug, ast_free, AST_PTHREADT_NULL, ast_tls_config::cafile, ast_tls_config::capath, ast_tls_config::certfile, ast_tls_config::cipher, ast_tcptls_session_args::master, ast_tcptls_session_args::name, NULL, ast_tcptls_session_args::old_tls_cfg, and ast_tls_config::pvtfile.
Referenced by __ast_http_load(), __init_manager(), manager_shutdown(), and unload_module().
◆ ast_tls_read_conf()
| int ast_tls_read_conf | ( | struct ast_tls_config * | tls_cfg, |
| struct ast_tcptls_session_args * | tls_desc, | ||
| const char * | varname, | ||
| const char * | value | ||
| ) |
Used to parse conf files containing tls/ssl options.
Definition at line 875 of file tcptls.c.
References ast_clear_flag, ast_free, ast_log, ast_parse_arg(), ast_set2_flag, ast_set_flag, AST_SSL_DISABLE_TLSV1, AST_SSL_DISABLE_TLSV11, AST_SSL_DISABLE_TLSV12, AST_SSL_DONT_VERIFY_SERVER, AST_SSL_SERVER_CIPHER_ORDER, AST_SSL_SSLV2_CLIENT, AST_SSL_SSLV3_CLIENT, AST_SSL_TLSV1_CLIENT, AST_SSL_VERIFY_CLIENT, ast_strdup, ast_true(), ast_tls_config::cafile, ast_tls_config::capath, ast_tls_config::certfile, ast_tls_config::cipher, ast_tls_config::enabled, ast_tls_config::flags, ast_tcptls_session_args::local_address, LOG_ERROR, PARSE_ADDR, and ast_tls_config::pvtfile.
Referenced by __ast_http_load(), __init_manager(), and reload_config().
◆ check_tcptls_cert_name()
|
static |
Definition at line 85 of file tcptls.c.
References ast_debug, ast_log, LOG_WARNING, and str.
Referenced by handle_tcptls_connection().
◆ handle_tcptls_connection()
|
static |
creates a FILE * from the fd passed by the accept thread. This operation is potentially expensive (certificate verification), so we do it in the child thread context.
- Note
- must decrement ref count before returning NULL on error
Definition at line 140 of file tcptls.c.
References ao2_ref, ast_iostream_get_ssl(), ast_iostream_start_tls(), ast_log, ast_sockaddr_stringify(), AST_SSL_DONT_VERIFY_SERVER, AST_SSL_IGNORE_COMMON_NAME, AST_SSL_VERIFY_CLIENT, ast_tcptls_close_session_file(), ast_test_flag, ast_thread_inhibit_escalations(), ast_thread_user_interface_set(), check_tcptls_cert_name(), ast_tcptls_session_instance::client, ast_tls_config::flags, ast_tcptls_session_args::hostname, LOG_ERROR, name, NULL, ast_tcptls_session_instance::parent, ast_tcptls_session_instance::remote_address, ast_tls_config::ssl_ctx, str, ast_tcptls_session_instance::stream, ast_tcptls_session_args::tls_cfg, and ast_tcptls_session_args::worker_fn.
Referenced by ast_tcptls_client_start(), and ast_tcptls_server_root().
◆ session_instance_destructor()
|
static |
Definition at line 72 of file tcptls.c.
References ao2_cleanup, ast_free, ast_iostream_close(), NULL, ast_tcptls_session_instance::overflow_buf, ast_tcptls_session_instance::private_data, and ast_tcptls_session_instance::stream.
Referenced by ast_tcptls_client_create(), and ast_tcptls_server_root().
◆ write_openssl_error_to_log()
|
static |
Definition at line 111 of file tcptls.c.
References ast_free, ast_log, and LOG_ERROR.
Referenced by __ssl_setup(), and __ssl_setup_certs().
 1.8.13
1.8.13